Unique expertise at the intersection of data science, public policy & emerging technologies!
Gavin Rozzi is an award-winning data scientist, web developer & former independent journalist who has created several successful local news websites and open-source civic information platforms serving New Jersey.
Rozzi is currently a data scientist with a background in public policy research and education. He has a unique blend of skills and experience that enables him to drive value through data-driven decision making. With a strong track record of success in data analytics and a commitment to staying at the forefront of emerging technologies, he has consistently delivered valuable insights and driven results for a wide range of organizations.
Rozzi has a particular expertise in leveraging public sector datasets to inform policy and decision making, and has developed a reputation as a technical leader in this area. He is skilled at implementing new and emerging technologies in a way that creates value, and has a track record of success in this area. In addition, he has expertise in leveraging spatial data for location-based insights and has received awards for his visualization design. He is also skilled in developing interactive web applications that leverage data to deliver powerful insights and experiences for users.
- Open source civic tech
- Public policy analytics
- Data science for public good
- R & Python development
M.S., Data Science & Strategic Analytics, 2020
Stockton University
B.A., Political Science, 2018
Stockton University
Recent Posts

Imagine a world where your every online utterance is subject to censorship by powerful tech companies and governmental entities. This is the reality that we may soon face if attempts to roll back Section 230 protections are successful.
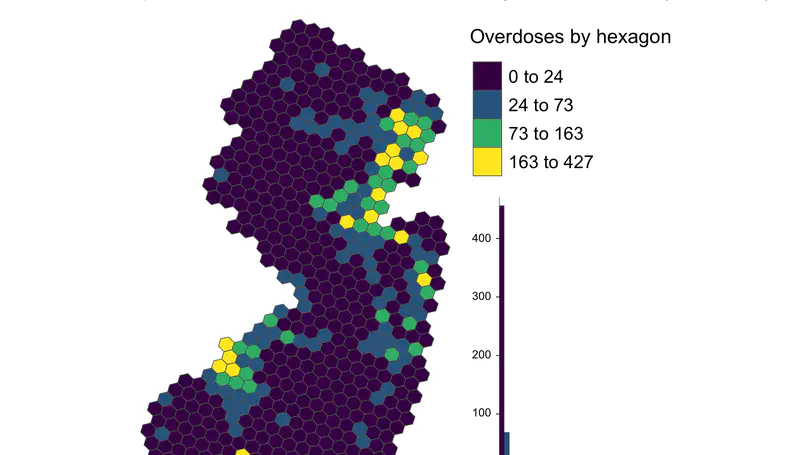
State administrative data is a valuable resource for identifying New Jersey communities impacted by the opiate crisis. In this post I present some initial results from 3 years of data collected under a state Attorney General’s Office directive.
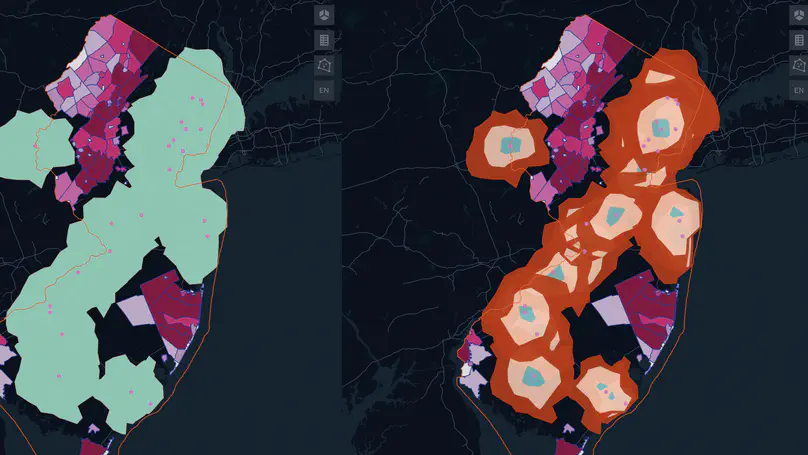
Despite the state’s progress on expansion of adult recreational use and medical cannabis, one third of New Jersey counties lack access to even a single dispensary. This post presents a spatial analysis of New Jersey’s medical cannabis dispensary focusing how far residents must travel to obtain cannabis in the state.